Until recently, most Cloud Service Providers (CSPs) were mostly occupied with delivering data storage and cloud storage facilities to businesses, with no attention paid to the reliability of the data or whether it followed industry regulations. As the cloud landscape evolves and becomes more dynamic, CSPs are becoming more mindful of how to assist consumers in achieving cloud enforcement, as well as the safest way to adhere to current rules and compliance changes.
Since cloud providers are being used on a national scale, their activities must be carefully supervised and in accordance with local legislation to ensure the protection of their data. It is critical to ensure compliance with regulations such as PCI, HIPAA, SOC 2, GDPR, CCPA, and others, particularly if your organization uses a variety of cloud providers with multi-faceted features. Although regulations vary by sector, determining if the platforms you use are consistent with the relevant legislation should be part of your cloud protection plan for 2021.
Maintaining enforcement can seem to be a difficult challenge with national and industry legislation on how you store data in the cloud continuously evolving and being revised. We’ve put together four performance factors for achieving cloud enforcement.
How the cloud can help resolve your compliance issues
Anyone who has worked in compliance can attest that it can be difficult and time-consuming. It also includes screenshots, spreadsheets, and other time-consuming (and uninteresting) activities.
So how does the cloud change traditional approaches to compliance and security? How does leveraging cloud services save the business time, stress, and potential legal fines for noncompliance? Let’s have a peek.
Shared Responsibility Model
The shared responsibility concept provides a situation in which the customer is no longer solely responsible for all security measures from their applicable frameworks. Instead, some are met by the cloud service provider (CSP), while some are shared controls between the CSP and the customer, while even some are left to the consumer.
Many of these compliance controls imply capital commitments, costs, and resource expenditures in terms of both time and personnel. By using the mutual accountability model, you will lean into the CSP to benefit from the vast investments they have made at scale, servicing thousands of consumers globally under every compliance system imaginable.
IaaS Compliance
In the Infrastructure-as-a-Service (IaaS) model, for example, enterprises no longer need to be concerned with the actual physical infrastructure, hardware, and security measures.
PaaS Compliance
Taken a step forward, with Platform-as-a-Service (PaaS), enterprises should use controlled services to prevent not only being concerned with the actual infrastructure, but also the operating systems and their related upgrade and upgrade cycles, which is a burden for many organizations, and exploiting bugs with fixes available is a common phenomenon.
SaaS Compliance
Finally, at the Software-as-a-Service (SaaS) layer, businesses do not need to concern about hardware, operating systems, or software development; instead, they merely consume usable software to sustain their business operations. Each layer of abstraction in the consumption model comes with a tradeoff of less power but also less accountability, which is an important factor for companies depending on their risk tolerance.
Compliance-as-Code
If you could only do one thing to reduce risk and optimize profits, it would be compliance-as-code.
Compliance-as-code entails specifying the compliance criteria in a vocabulary that is both human- and machine-readable. Configurations will then be deployed, checked, tracked, and reported automatically through the entire IT assets.
You can run one Inspec test through 100,000 servers in a single day and learn more about your enforcement and risk posture than the security team has in the previous ten years.
Let’s be clear about what compliance-as-code will add to the company.
1) Always be aware of what is going on with your IT estate and report any issues immediately.
2) Assist both the risk and growth departments in doing their work more effectively and efficiently.
3) Compliance-as-code assists businesses with articulating what it takes to go to production. When everybody understands what “done” looks like and the status of the distribution pipeline, the road to output is straightforward.
4) Automate the low-hanging fruit, and your security staff will move from a disciplinary role to an auditing function. Almost security-as-a-service!
5) Reduce the greatest security bottleneck: make requirements easy to absorb.
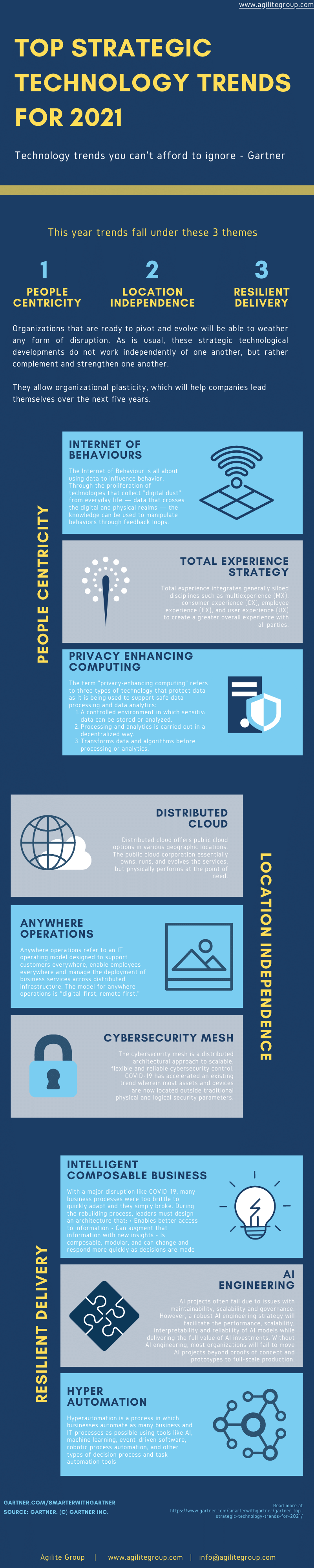
Compliance and emerging technology
When technological advances such as 5G, IoT, blockchain, AI, and others become more common, regulatory bodies become more interested in identifying the risks and putting them into the purview of current legislation or implementing new regulations. A team of researchers, for example, has created a prototype IoT protection and privacy label in the form of a “protein label.” Although this is not yet a regulatory mandate, businesses that use such technology should keep their eyes and ears open for regulatory signals.
Possible cloud enforcement options to explore
Leading service providers like AWS and Azure have developed robust compliance offerings that are worth investigating, as do emerging third-party SaaS offerings like ByteChek, which combine diverse market experience and multi-cloud integrations to really bring value to consumers.
Conformance Packs are a type of service provided by AWS. There are lists of AWS Config Rules and remediation steps that you can quickly install into your AWS accounts, domains, and AWS Organizations as a single agency. These are YAML models that include a variety of AWS controlled and custom rules, as well as remediation steps. Controls for systems such as CIS, DoD’s emerging CMMC, FedRAMP, NIST 800-53, HIPAA, AWS’s own operational/security best practices, among others are included in the templates.
AWS has also recently introduced AWS Audit Manager, which aids in the continuous auditing of AWS usage, proof gathering, and the reduction of manual efforts. It can use pre-built systems such as NIST 800-53, CIS Benchmarks, FedRAMP, GDPR, and others, as well as custom frameworks and controls tailored to the organization’s specific needs. It can then be used to generate audit-ready compliance reports.
The “Regulatory Compliance Dashboard” has been created by Azure’s Security Center. This demonstrates the conformity with selected compliance criteria as well as all of their related specifications, as mapped to relevant security evaluations. You can not only see compliance in the UI dashboard, but you can also download PDF files detailing your latest compliance posture with different systems such as SOC, CIS, PCI DSS, NIST 800-53, and more. You will then resolve non-compliant products to improve the compliance score.